Networking has evolved: extinction beckons for VPNs
There was a time when companies such as Blackberry and Nokia made the coolest portable communications devices around. Then, one day, everything changed. Apple’s iPhone reimagined how mobile phones were perceived and rival vendors that didn’t adapt, didn’t survive.
Other established technologies have had a similar fate: from laptops to data centres, SSDs have displaced hard drives. The cathode ray tube, gracing living rooms and desktops for the best part of 60 years, replaced by larger, slimmer, lighter and brighter flat screen LED displays.
It’s a form of tech Darwinism and it’s not just devices that become extinct, survival of the fittest extends to software too. And when it comes to natural selection, next in line to fade from view must surely be the Virtual Private Network (VPN). Yes, VPNs are more popular than ever, but so were Nokia and Blackberry phones, until something better came along.
In the beginning…
Dating back to 1996 and credited to Microsoft, VPNs deploy tunnelling tech that enables a reasonably secure form of network connectivity that has become widely adopted by remote workers and privacy-conscious internet users. Moreover, VPNs can wear a number of different hats and, for private browsing purposes, most will connect to a service that will use a different IP address to anonymise your online activity.
This might work for some but has its quirks. Often the substitute IP address will suggest you’re in a different geographical location, resulting in web pages showing up in foreign languages. Also, the bank now thinks you’re a hacker, if you try to get into your online account. Simply deactivate the VPN for certain tasks, and you’ll be fine – maybe.
Widely used in corporate environments VPNs enable a range of services, from remote desktop access to linking to off-site disaster recovery facilities. For remote desktop services, many businesses will rely on the public internet for connectivity and configure VPN access for each user. Even if the company sysadmins are competent at on-boarding users, VPN faults are difficult to trace and the public internet has plenty of its own quirks, with latency being a big headache.
Private enterprise
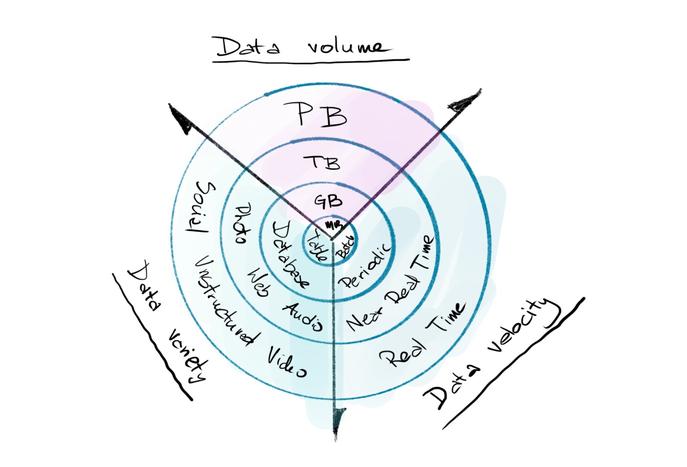
Aimed at corporates, multi-protocol label switching (MPLS) is an alternative network that’s certainly more capable and consistent than the public internet. Developed in the mid-1990s, with initial deployments appearing around the same time as early VPNs, MPLS offers a level of transparency that enables an enterprise WAN to be accessible in multiple locations and frequently involves MPLS-specific VPNs. To minimise congestion and sustain high bandwidth performance, MPLS sidesteps the public internet and, instead, relies on dedicated private lines for connectivity. As such, provisioning is costly and can take an age.
Also, global deployments will need to rely on multiple providers to enable an end-to-end MPLS network, which can bring with it service and security headaches that really shouldn’t be dogging such an expensive infrastructure solution. Moreover, with companies increasingly utilising cloud-based services, traffic inefficiencies are introduced as a consequence of the MPLS-based ‘hub and spoke' networking model.
Lay lines
When it comes to alternatives, perhaps a software-defined wide area network (SD-WAN) is the answer? While SD-WAN potentially lowers cost by utilising the public internet, the trade-off is it cannot offer the performance guarantees of a dedicated MPLS network. That said, SD-WAN is more of a management service, that can combine multiple networking technologies including MPLS. SD-WAN is described as a software ‘overlay’. By contrast, MPLS, with its hardware infrastructure, is an ‘underlay’. In its hybrid configurations, SD-WAN can help overcome some of the aforementioned traffic inefficiencies of backhaul performance overheads for tasks such as accessing cloud services. However, when it comes to remote users and operations, access via a VPN is de rigueur.
In sum, software management of different networking protocols still rely upon legacy VPN technology to connect users and internet connectivity for the SD-WAN to control the whole network, which still incurs latency. SD-WAN’s capabilities may well suit corporate entities with a diverse networking infrastructure but, in endeavoring to be all-encompassing, SD-WAN requires considerable technical expertise and comes at a price that is beyond the reach of many businesses with more modest needs.
The killer app
If networking were to truly evolve it would move beyond these constraints of cost and complexity, but what would it look like? Ideally it would perform invisibly and securely, wherever you happened to be located. The experience would be identical to using the office local area network (LAN), enabling access to the same resources but with consistent performance and minimal latency, all possible using its unique overlay via the public internet. Remote users would be part of a Virtual Extended Network (VEN) featuring end-to-end encryption, and safeguarded by standard LAN security protocols, protecting both the network and securing device endpoints.
The Virtual Extended Network can be thought of here as an evolutionary step in software-defined networking (SDN) technology, which has previously been confined to LAN environments. Scalable, affordable, easy to configure and available for enterprise or as a managed cloud option, user computers or mobiles would simply need a lightweight background app to connect. Even global facilities could connect with ease and behave as one, with lower costs linking to disaster recovery sites configured for failover switching being one of the many additional capabilities.
Actually, the Virtual Extended Network does exist – designed and developed in the UK, the home of Darwin. VPNs are destined to become a dying breed; networking has evolved, and natural selection is thriving out in the wild already. The origin of this species is to be found in industrial, educational and local authority environments. And very recently, a quantum-encrypted option for intelligence services and financial institutions has appeared, all part of the evolution of the Virtual Extended Network.
David Sweet,CEO of iQuila